Jasjeet Singh, Senior Principal Consultant, DNV
03/03/2026 | Offshore wind
Securing the North Sea: engineering cyber resilience into offshore wind
DNV is a leading provider of technical safety and cyber security services to the energy industry across the globe. In particular, DNV play a key role in strengthening maritime security and cyber resilience across the North Sea by helping operators protect increasingly digitalised offshore assets from evolving hybrid threats and cyber attacks. As ships and offshore units become more interconnected, DNV work with industry to ensure that both information technology (IT) and operational technology (OT) systems are protected, supporting the design, testing, and verification of cyber secure maritime systems and providing guidance aligned with international regulations. Our work highlights the growing risks to navigation, positioning, and seabed infrastructure, especially as state sponsored and criminal actors increasingly target critical offshore energy and data flows.
Ahead of RenewableUK's Cyber & Security 2026, which DNV is proud to be sponsoring, this article brings together DNV’s experience in the area and sheds a light on key challenges and lessons learned from cyber incidents in the offshore wind industry.
Cyber & Security 2026
Setting the scene
The North Sea’s offshore wind capacity will continue to expand over the coming decade. The rapid rollout of offshore wind in the UK and North Sea countries is advancing net zero goals, making energy systems more interconnected and digital, but also increasing vulnerability to cyber and hybrid threats. Digital optimisation and connectivity will deepen. If cyber resilience does not scale with physical and market integration, systemic risk will scale with it.
Although this is a multifaceted and complex framework to work within, this article will focus on the modern cyber threat landscape, real-world incidents relevant to the UK and North Sea, policy and regulatory direction (particularly UK maritime security strategy), engineering actions for asset owners, and finally, how AI can enhance defensive capacity.
The evolving cyber threat landscape
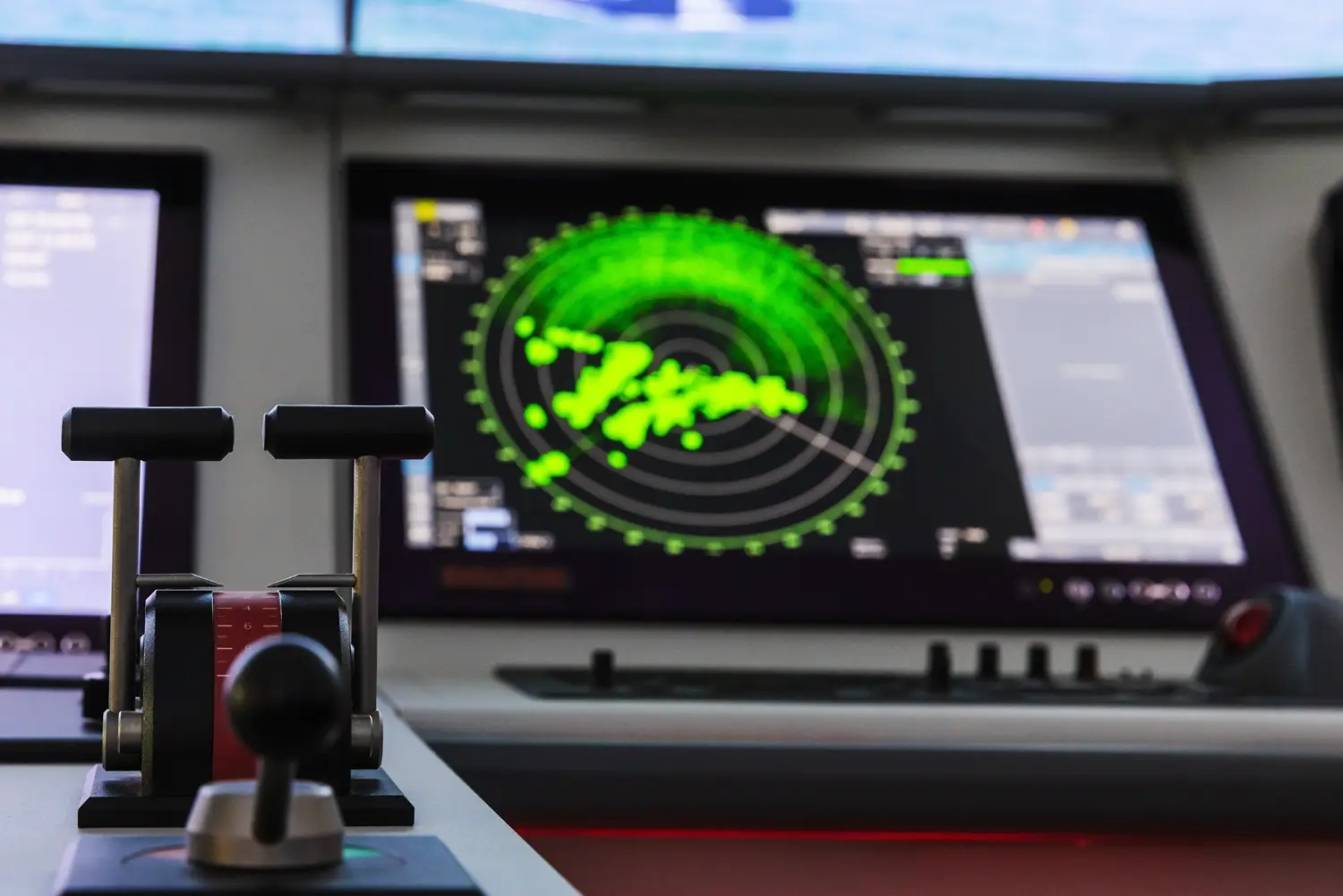
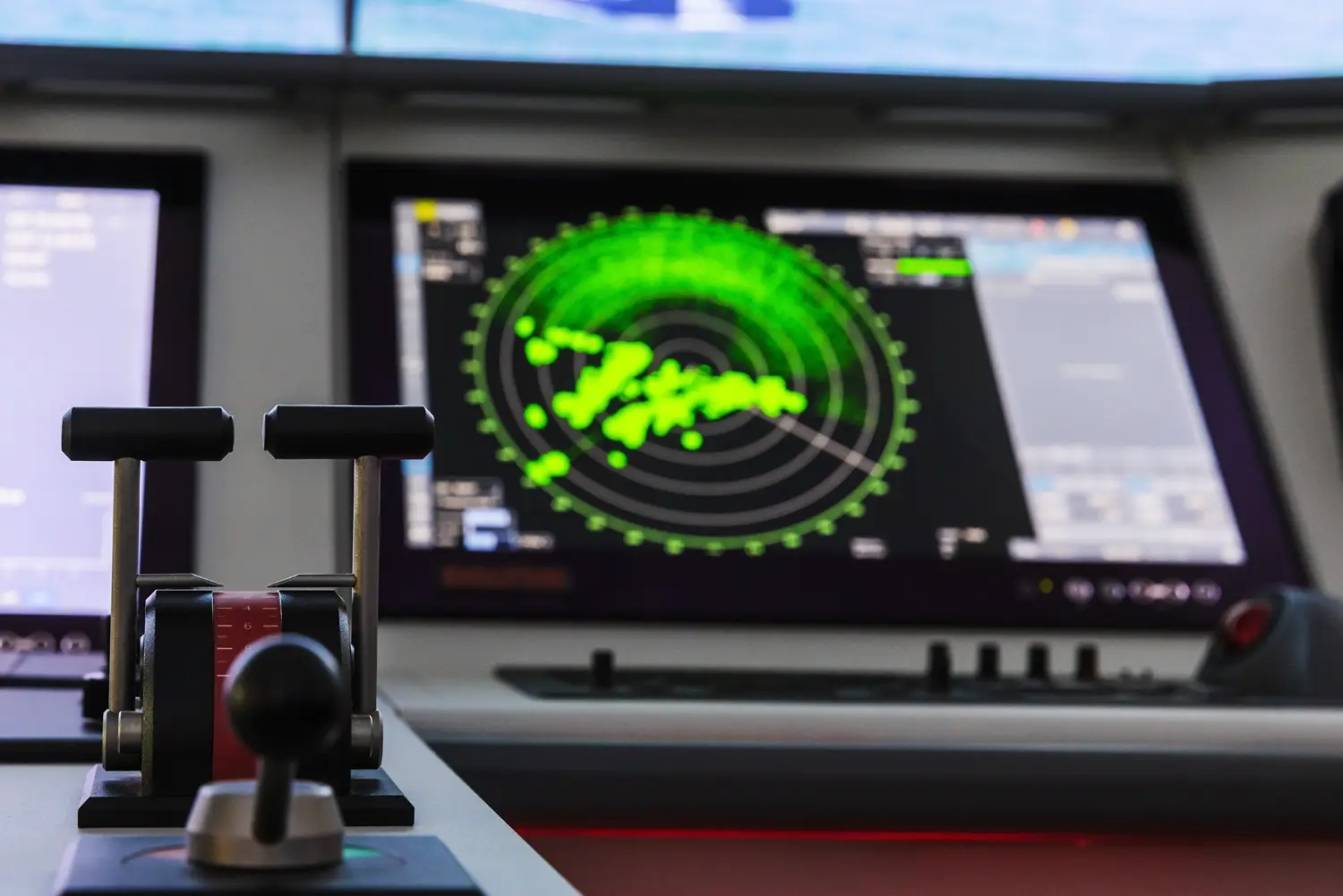
Today’s offshore wind farms and subsea assets are cyber-physical systems comprising:
- Programmable logic controllers (PLCs) in turbines
- Supervisory Control and Data Acquisition (SCADA) and energy management systems
- HVDC converter stations with complex digital controls
- Remote communications links (satellite, microwave, fibre)
- Cloud-hosted analytics and vendor access mechanisms
Although the integration of IT and OT is seen as a positive and necessary step to reach higher levels of control and digitalisation it also expands the attack surface and introduces systemic risk across engineering, operations and supply chains. Some of the key threats in the North Sea context include state-aligned threat actors (conducting reconnaissance and pre-positioning access against energy infrastructure) or ransomware operators (targeting corporate IT with potential impact on OT environments), as well as potentially non-malicious but ultimately disruptive stakeholders introducing operational errors. The vectors themselves can also be quite varied as risks can appear through compromising the supply chain (e.g. through software/firmware tampering or credential abuse), ranging through to more direct actions such as global navigation satellite system (GNSS) / GPS spoofing, thus affecting timing and maritime positioning. Ultimately hybrid tactics blending cyber engagement with physical surveillance and maritime probing are a key concern in this context while at the same time, the dense web of cross-border HVDC links and offshore clusters means that disruption in one part of the system can have cascading effects across markets and jurisdictions.
Policy and regulatory direction: the UK maritime security framework
The UK’s National Strategy for Maritime Security (NSMS) sets out a whole-of-government approach to maritime security over a five-year horizon. This strategy explicitly recognises technology, innovation and cyber security as essential to protecting maritime infrastructure, including seabed and undersea facilities that support energy transmission. What is important to note is that this cross-departmental strategy signals that maritime cyber risk is not an isolated IT concern, but a national security and infrastructure priority. Reflecting this realisation, the key strategic objectives go beyond protecting borders, ports and maritime infrastructure to supporting a secure, resilient ocean by improving data and situational awareness, technology coordination and integrated capability across defence, law enforcement and industry.
UK and North Sea incidents: lessons learned
Maritime cyber disruption from the NotPetya virus: Maersk
In 2017, shipping company Maersk was hit by the NotPetya ransomware attack, which reverberated through port operations and logistics chains that support offshore energy infrastructure. Ports serving North Sea wind installation and maintenance operations experienced disruption due to compromised IT systems. While turbines and grid assets weren’t directly attacked, the incident highlighted a systemic risk, namely that if maritime logistics and digitally coordinated vessel operations are disrupted, offshore commissioning, subsea cable repairs, and maintenance campaigns can be delayed or halted.
This incident reinforces a critical point for offshore wind operators: energy and maritime cyber resilience are interdependent systems.
UK energy systems: Elexon ransomware incident
In 2020, Elexon, which oversees the UK’s Balancing and Settlement Code, suffered a ransomware incident affecting internal systems. Although physical grid operations continued, the event demonstrated that market and dispatch platforms are integral to operational continuity, while also showing that corporate cyber incidents can indirectly affect generation and revenue. This instance shows that strong segmentation between corporate and operational environments is essential for resilience; this in turns means that for offshore wind and HVDC operators, protecting commercial platforms and market-related systems is as important as protecting turbines and converters.
What offshore asset owners should do now
For owners and operators of offshore wind farms, HVDC platforms, subsea cables and associated infrastructure, resilience must be engineered in. Steps that can be taken at system design level include creating architect for IT/OT Segmentation (e.g. rigorous network separation and zero-trust remote access) and hardening of OT and control environments (passive monitoring of industrial protocols through to baseline behavioural models for the system components and Immutable, offline backups). It is key that any such steps are also tested: segmentation of architecture should be validated with penetration tests and red team exercises, while technical assurance must be demonstrable and updated throughout asset life cycles.
How AI can strengthen offshore cyber defence
When governed with appropriate controls, AI systems can materially enhance cyber defence. Although this is rapidly developing field, approaches such as automated anomaly detection through machine learning that can detect deviations in component and system behaviour can be crucial in identifying threats that would currently elude rule-based monitoring. Similarly cross-domain threat correlation would mean that AI can collect information from a variety of sources (telemetry, vessel tracking, satellite indicators, and threat intelligence) therefore aiding the detection of coordinated hybrid threats. At the other end of the scale, AI-assisted verification can compare predicted mechanical performance with reported sensor data to identify data manipulation or spoofing.
Most interestingly however, AI can provide assisted containment and response, leading to rapid network isolation and trigger safe-mode transitions, supplementing or in time even surpassing, human-led response.
For this to work however, engineering governance is essential. AI must be transparent, auditable, and integrated within human decision loops.
DNV is leading the way with developing assurance frameworks for the use of AI in industrial contexts, and sees the application of AI in the context of cyber and physical defence offshore as a key area where it can leverage its knowledge of assurance systems, its maritime experience and its market-leading cybersecurity capabilities.
Final thoughts
Although this article has provided a snapshot of the current status of domains, their associated risks and potential developments, it is important to remember that this is a fast-evolving and ever-changing tapestry of interconnected parts. As such, any approach to security must also look to be as dynamic and flexible as the threat vectors presenting themselves. It is key to remember however that resilience is not a compliance checkbox. It is a strategic enabler of a secure, dependable energy transition.
If you want to learn more about future-proofing North Sea assets against physical and cyber attacks, I'll be discussing this on panel session A5 with colleagues at RenewableUK's Cyber & Security 2026.



